- WELCOME
- FOREWORD
- EXECUTIVE SUMMARY
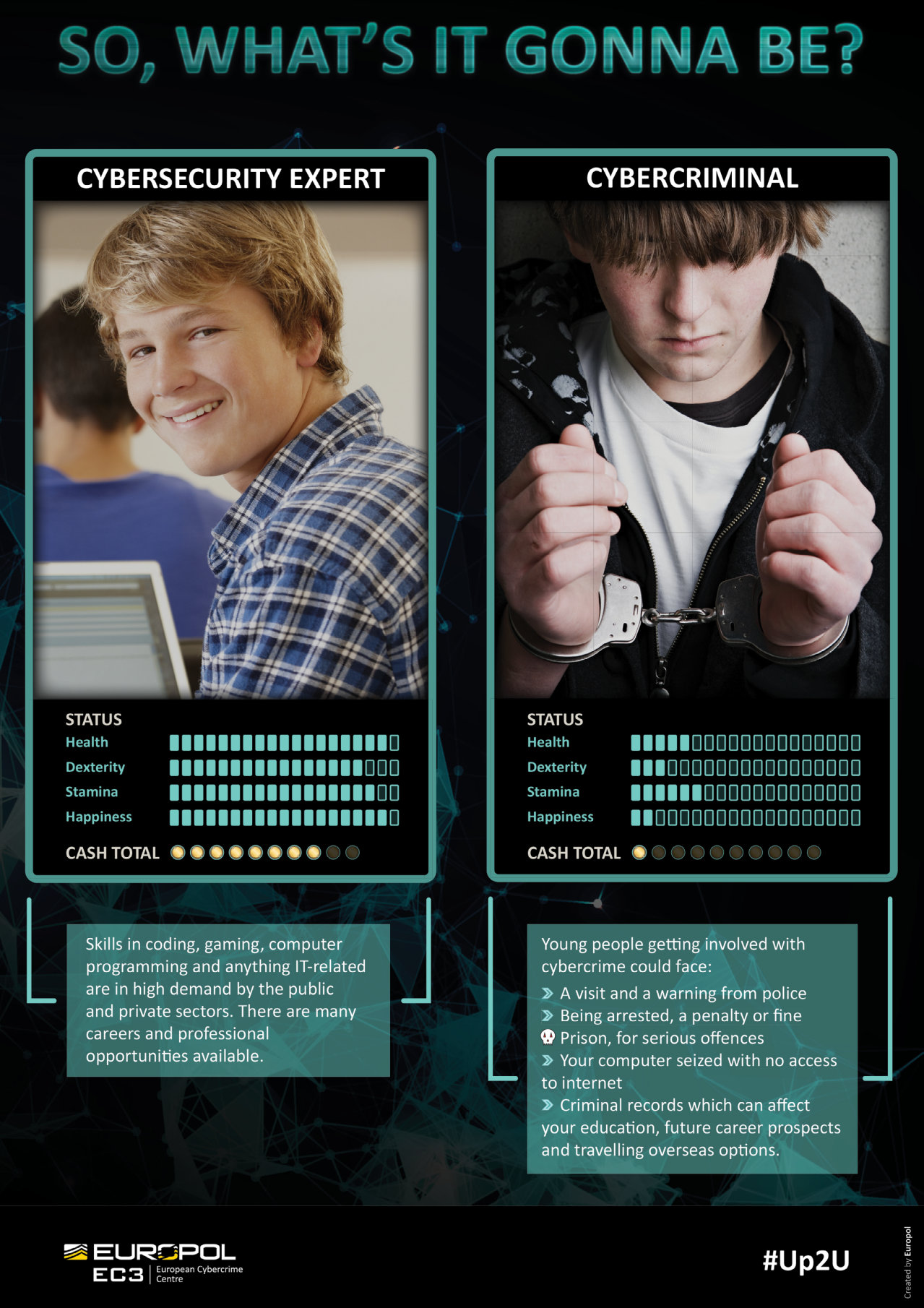
- CRIME PRIORITY: CYBER-DEPENDENT CRIME
- CRIME PRIORITY: CHILD SEXUAL EXPLOITATION ONLINE
- CRIME PRIORITY: PAYMENT FRAUD
- CRIME PRIORITY: ONLINE CRIMINAL MARKETS
- THE CONVERGENCE OF CYBER AND TERRORISM
- CROSS-CUTTING CRIME FACTORS
- THE GEOGRAPHIC DISTRIBUTION OF CYBERCRIME