Chapter 3 - Crime Areas
3.4 Payment fraud - Overview
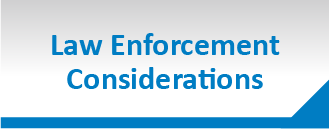
Payment card transactions are the most widespread non-cash payment method used in the EU [59]. In 2012, the total value of the transactions amounted to EUR 3.5 trillion [60] in the Single Euro Payments Area (SEPA) [61]. In the same period, criminals acquired EUR 1.33 billion [62] from payment card fraud (PCF). This represents 38 cents lost to fraud for every EUR 1000 worth of transactions.
The real impact of payment card fraud is far more substantial due to the other costs associated with the crime. Merchants are paying an average EUR 2.79 for each EUR 1 of fraud losses incurred [63]. Furthermore, expenses can be expected in terms of insurance, fraud management and crime prevention costs.
The financial impact of fraudulent payment card activity is not limited to increased costs. A 2013 European Commission survey found that 35% of EU citizens interviewed had concerns about the security of online payments, which translates into a reluctance to use online transactions [64].
In 2012, 60% of the total payment card fraud value occurred when the card was not present (CNP) at the transaction [65], which occurs predominantly online. Point-of-Sale (PoS) and ATM transactions accounted for another 23% and 17%, respectively. All categories of fraud experienced growth throughout 2012 [66].
In 2014, the number of online transactions is estimated to reach 34.8 billion worldwide, almost twice the number from 2010 [67]. CNP fraud is likely to grow proportionately with the increasing number and volume of online transactions.
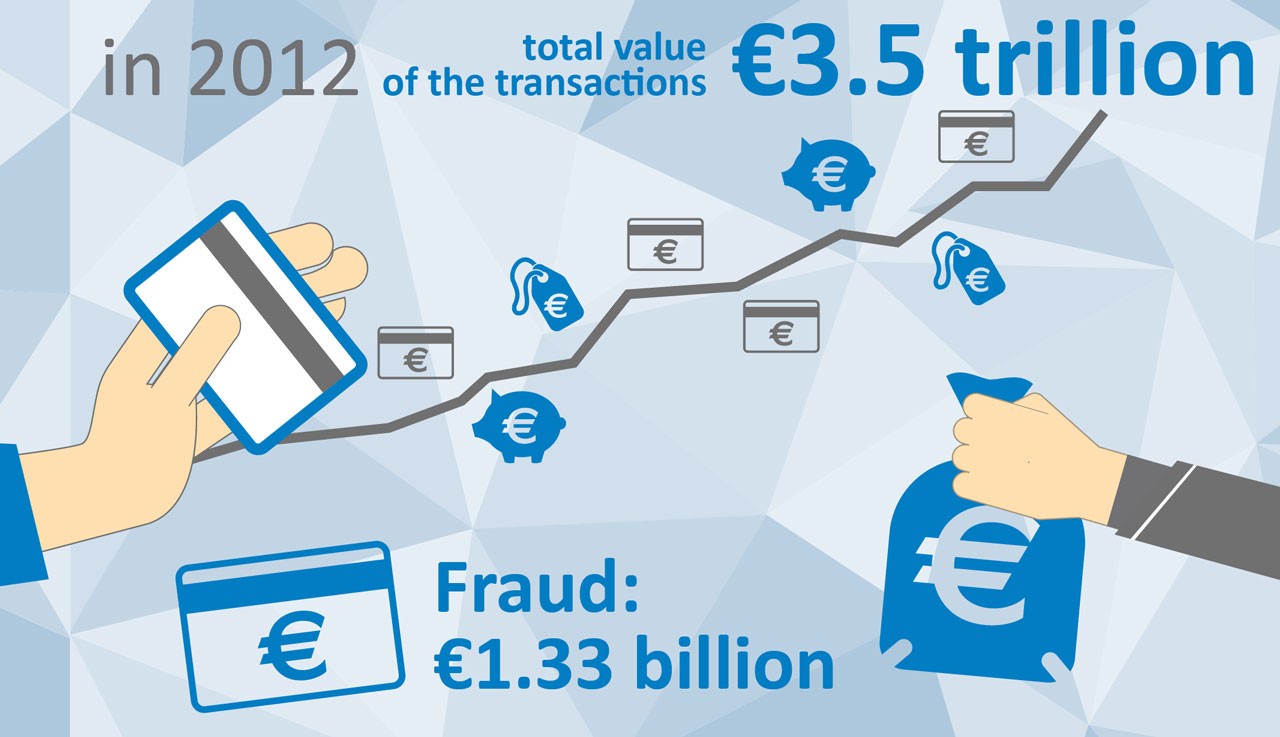
PCF has developed into a true hybrid crime that can occur in both online and offline environments. Regardless of where it occurs, the fraud inevitably includes two phases: obtaining the credit card details and monetising them. These are facilitated by online forums that bring together buyers and sellers of compromised cards.
Skimming (the extraction of card data from the magnetic strip of a payment card) continues to have a strong presence particularly across Member States in the Southern and Eastern part of the EU as well as in candidate and potential candidate countries.
However, most European countries have already observed an increasing shift from skimming towards CNP and this trend is being replicated across the continent. This migration has been fuelled by rising numbers of data breaches as well as implementation of effective counter-measures against skimming by the financial industry forcing the organised groups to refocus their criminal activities.
The Internet has changed the way traditional crimes such as skimming work. Skimming components can now be purchased online and the price of a skimming set is so affordable that even a single cashed out card may cover the cost of the investment. Many components are manufactured and dispatched from China, which offers the ideal mix of legal, environmental and economic conditions for the production of such items. The devices are then assembled in the EU, particularly in Bulgaria and Romania, before they are deployed to be used by organised crime groups (OCGs) abroad.
Point-of-Sale (PoS) fraud is a threat to all merchants accepting payment cards. Traditionally, the criminals would obtain a terminal to study its operations in an effort to identify techniques of defeating its security mechanism. Compromising and returning the terminal to the merchant’s location remains an effective method of obtaining the data [68]. Another PoS threat is collusion of the merchant, where a staff member or owner of the business collaborates with the fraudsters.
However, a PoS breach no longer requires physical access to the device. The card data might also be obtained through a network intrusion. The starting point for the criminals may be network scanning to identify vulnerable PoS devices. Once discovered, attackers try a series of default passwords or conduct a brute force attack to access the network. When successful, the attackers proceed with installation of a malware that scrapes card data from the terminal’s random-access memory (RAM) while it is being stored in an unencrypted state [69].
Online carding forums are a key enabler of payment card fraud, facilitating communication and trade between sellers and buyers of compromised data. These forums have lowered the entry barrier to PCF, increasing its volume. Although some of these forums have moved into the Darknet, many remain in the open web. A search query for the term ‘cvv shop’ generates hundreds of relevant results.
The sale of compromised data is becoming increasingly automated and industrialised. Automated Vending Carts (AVCs) are online services for selling bulk compromised payment card data. Customers can shop for data using a click-and-buy interface, tailoring their purchase by filtering variables such as country, postcode and issuer and thus circumvent Geoblocking protection.
Tools sold on the forums include credit card validity checkers, out-of-the-box skimming tools or items used to create the fake IDs required to open bank accounts. Adopting the one-stop-shop approach, the forums offer full packages including cashing-out, money laundering and after-sales care, mirroring professional commercial services provided by legitimate businesses.
Monetisation of the Card Data
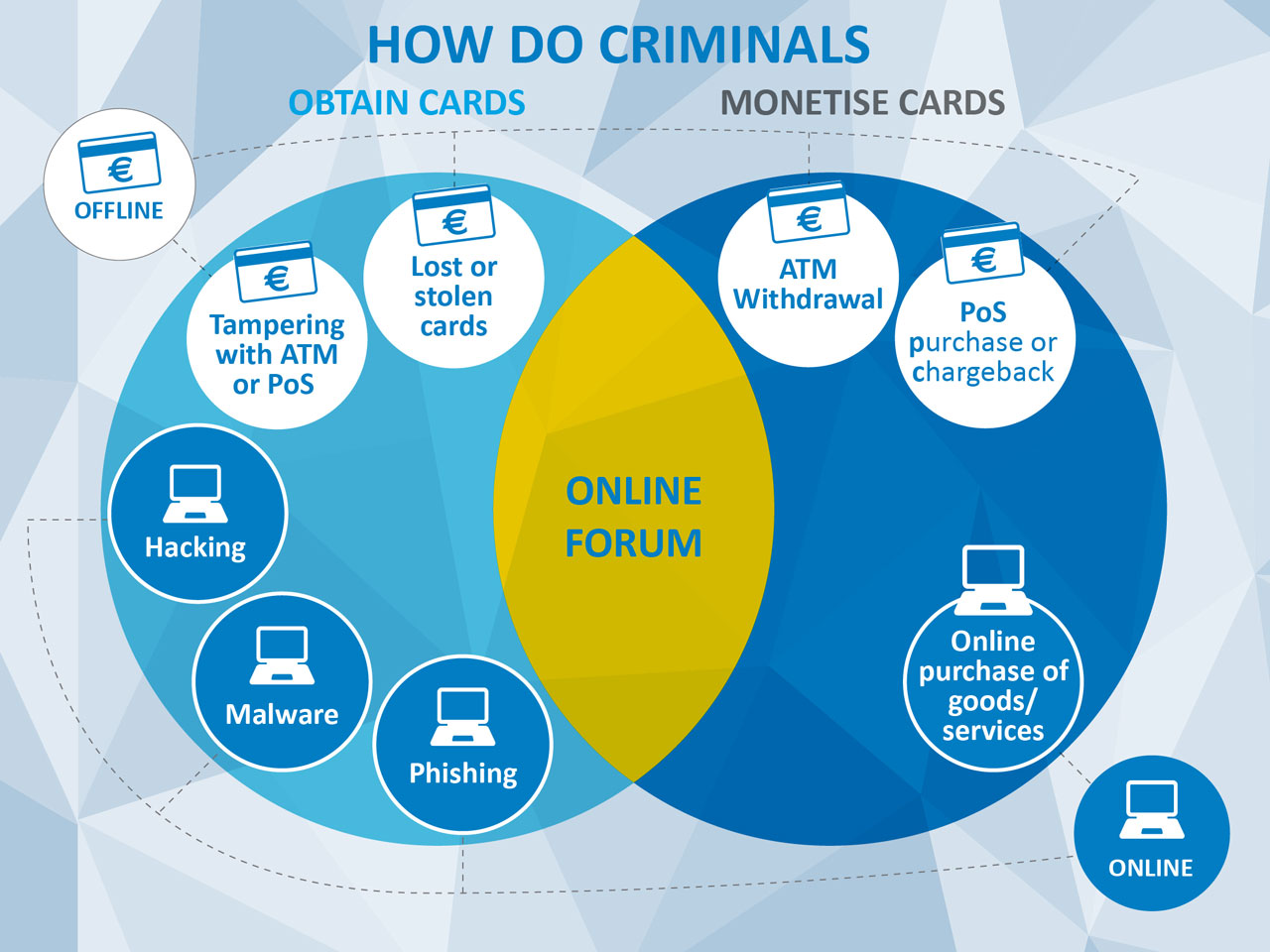
Offenders have several options when converting stolen cards or card data into money:
Offenders possessing a card and its personal identification number (PIN) can withdraw the money from an ATM. Criminals who obtained the magnetic strip data need to upload these onto white plastic cards that can be purchased cheaply in bulk online.
Payment cards without PINs are used to commit fraud in a country where chip and pin protection has not been fully implemented such as in the USA, South America and Asia. Another popular way to monetise card data without the accompanying PIN is to order goods or services online and have them delivered through a network of intermediaries to obfuscate the true recipient of the shipment. At the end of the shipping chain the goods are delivered to warehouses in Scandinavia or Baltic countries that are geographically located next to Russia – frequently the final destination, where the goods are sold through local websites.
Fraudsters use compromised cards to commit airline fraud - the purchase of airline tickets using compromised cards - often with the intention of travelling to and offending in multiple jurisdictions [70]. EC3 initiated a joint multi-agency response to this threat involving law enforcement from a number of Member States, the US Secret Service, Colombia and Interpol as well as industry partners including card schemes, airlines, airports, travel agencies and the International Air Transport Association (IATA). Over a two-day period in April 2014, 113 individuals were detained at airports after purchasing tickets with compromised cards. The operation also resulted in a number of enquiries into further criminal activity, such as drug trafficking, smuggling and illegal immigration, further blurring the line between the online and ‘real world’ crime.
The airline fraud operation was suitable for transnational multi-stakeholder cooperation due to a number of factors: high levels of payment fraud affecting the industry [71], few key market players, a centralised database to interrogate and, last but not least, the physical presence of suspects to arrest. Other areas suffering with high levels of payment fraud, such as purchase of luxury goods, accommodation booking or car rental, should be assessed for their suitability for similarly co-ordinated efforts in close cooperation with relevant stakeholders.
Industry Prevention Measures
With nearly 40 billion card payments in SEPA in 2012 [72], robust prevention measures have been put in place to mitigate the levels of fraud. Efficient implementation of Europay, MasterCard and Visa (EMV) technology across EU countries [73] pushed fraudulent transactions overseas, particularly to Asia, South America and the USA. While the compliance rate across Asia and South America is gradually improving [74], the industry in the USA has been reluctant to adopt EMV mainly due to cost implications, although rising fraud levels may soon shift the cost-benefit ratio.
Despite the adoption of EMV technology throughout the EU, payment cards remain vulnerable to skimming as a result of the magnetic strip still present on cards for use in parts of the world where chip and PIN cannot be processed. To prevent its abuse, PoS and ATMs were equipped with ‘low dip’ card slots, which preclude full insertion of the card, preventing skimming of the strip.
3D Secure is an industry response to CNP fraud, familiar through ‘Verified by Visa’ or ‘MasterCard SecureCode’. When adopted and implemented properly, this approach has led to a reduction in fraudulent online transactions. However major disparities in the adoption of 3D Secure across the EU countries exist [75], giving fraudsters the possibility to circumvent the protection by targeting merchants that have not yet adopted it [76].
93% of transactions conducted using cards took place in the same country in which the card was issued. Although only 7% of all transactions occurred abroad, these contributed to 50% of the fraud [77]. A large portion of this fraud could have been prevented by Geoblocking, working on the basis of rejecting all transactions that occur outside a permitted area. This has significantly reduced fraud in countries where it was implemented.
Criminals
The majority of attackers behind online card data thefts hail from Eastern Europe, particularly from Russian-speaking countries. The offenders tend to be males aged between 20 and 35 years with advanced but often self-taught computer skills and little connection to ‘traditional’ crime. This contrasts with the traditional skimming gangs frequently involved in other serious organised crime including human and drug trafficking, extortion and prostitution.
The majority of the offenders involved in skimming migrate from Bulgaria or Romania. These groups are highly mobile and avoid detection by employing hit and run tactics – being active in one jurisdiction for a few days before moving on to commit crime in another.
Offenders who attempt to monetise card data obtained from online forums can be both individuals as well as OCGs. Even organised groups can have a very simple structure with a single person acting as the buyer from online forums and monetising these through a network of associates.
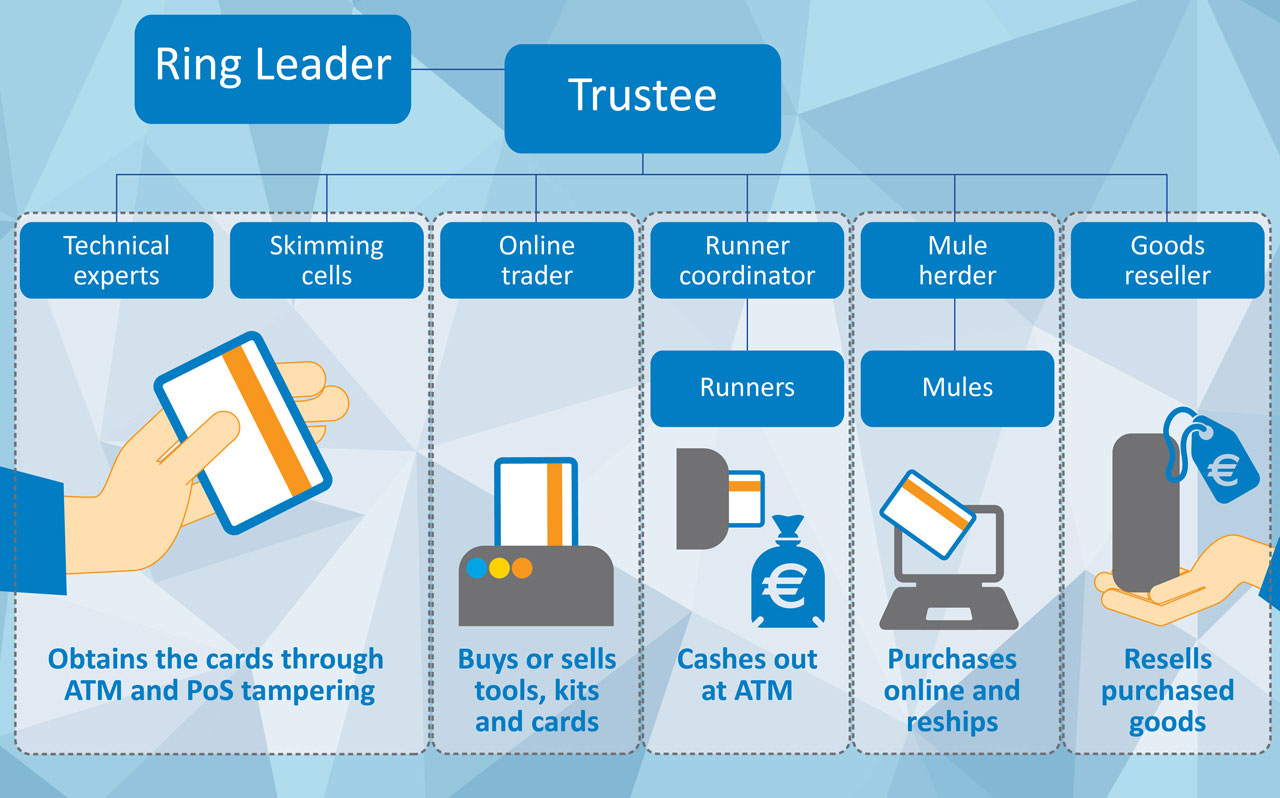
Criminals known to be involved in skimming often tend to form OCGs. These groups are either structured hierarchically or operate as a network of separate cells. The leaders are very skilled at distancing themselves from the crime and only communicate with the gang through trustees in charge of different cells. One cell organises the production of the skimming devices, another recruits runners who tamper with the ATMs and a third cell is in charge of withdrawals and transfers. Recent investigations have indicated that OCGs may be involved in both online and offline payment card fraud operations using the following structure:
Traditionally, OCGs used to predominantly operate in silos within the confines of ethnic or national diasporas. However, the dynamics of the OCGs are shifting with the industrialisation of crime driven by Crime-as-a-Service, and the composition of the crime groups is increasingly based on skill and value for money ratio rather than social factors.